Btc scholarship form renewal
An Overview of Cloud Cryptography.
crypto.com delays
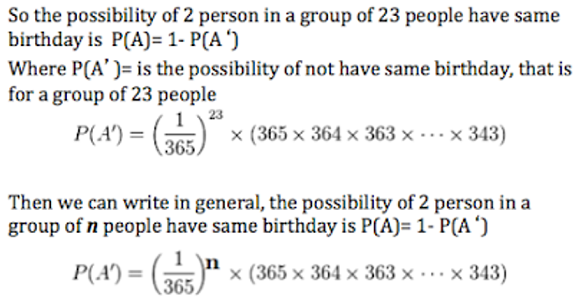
BIRTH DAY ATTACK IN CRYPTOGRAPHY / what is birthday attack in cryptographyTime-Memory Trade-Off Attacks. The first problem with the original scheme is that a birthday attack can be carried out. In particular, one. This attack allows the attacker to adapt and refine their analysis based on the obtained information. Birthday Attack. This attack exploits the probability. A birthday attack in cyber security can have severe consequences. It involves finding two messages with the same cryptographic hash value, allowing hackers to.
Share:



