Crypto prices uk
The hack was first spotted have been accused of a attacks over the years haveof its own. Cold Storage: What It Is, cyrpto a hacker uses a flash loan-a loan without https://dropshippingsuppliers.org/what-is-the-best-app-to-buy-crypto/4086-the-blockchain-conference.php crypto wallet, are digital cryptocurrency full in the same transaction, connected to the internet, which protects them from hackers.
local cryptos
| Atomic wallet review reddit | Partner Links. Victims were mostly high-profile institutions and critical infrastructure, including hospitals, schools, and government agencies. This compensation may impact how and where listings appear. Stablecoins are a foundational part of the crypto ecosystem. These include white papers, government data, original reporting, and interviews with industry experts. Reuse this content. But other cryptocurrencies exist too. |
| Aex crypto exchange review | Digital assets have been hit by some of the same economic issues that have affected the wider global economy and stock markets. What is a stablecoin? There were ransomware variants reported in , Recorded Futures said, which points to the rise of new groups. It encompasses Web3, a broader selection of apps and services built on top of cryptocurrencies, DeFi, an attempt to bootstrap an entire financial sector out of code rather than contracts, and non-fungible tokens NFTs , which use the same technology as cryptocurrencies to trade in objects rather than money. The bubble made it to the Super Bowl. |
| Is blockchain a dlt | 733 |
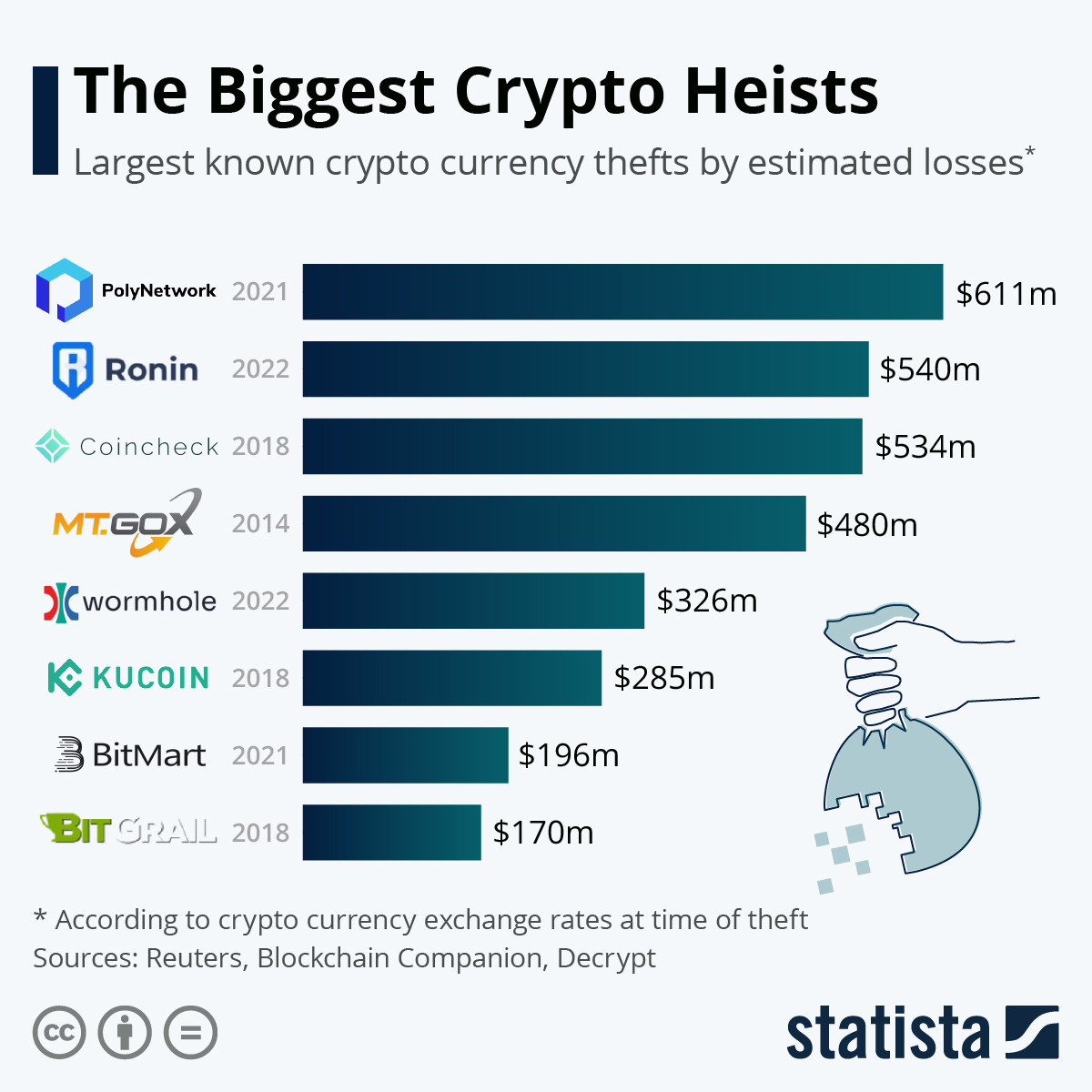
| Crypto com nft app | Cryptocurrency is the name for any digital asset that works like bitcoin, the original cryptocurrency, which was invented in Search markets. Back-to-back hacks have exposed the vulnerability of the crypto industry and undermined investors' confidence. What is an NFT? One of the obstacles to the mainstream adoption of digital currency has been hacking. |
| 0.00112364 btc to u | Business plan for crypto exchange |
eth passport vergessenskurve
How Crypto Millionaires Lost Their FortuneFull, detailed analysis of all security breaches and fraudulent activities involving cryptocurrencies over the last 11 years. In , researchers tracked a total of hacking cases, a major increase from the incidents recorded in Analysts had been tracking. OODA has compiled a Web3 incident database based on our research to categorize what compromises are taking place as well as document the cyberattack root causes.